Req 3a — Systems to Protect
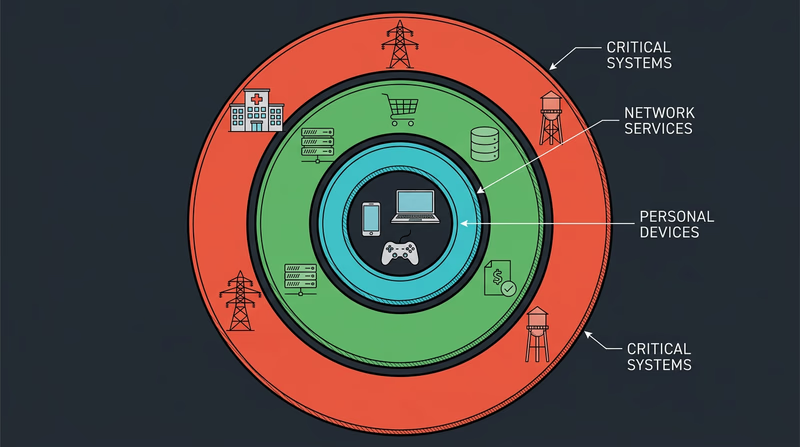
When most people hear “computer system,” they think of a laptop or desktop. But the reality is far bigger. Computer systems run hospitals, control traffic lights, purify drinking water, and fly airplanes. When these systems get attacked, the consequences go way beyond a frozen screen or lost files — people’s lives can be at risk.
What Counts as a “Computer System”?
A computer system is any combination of hardware, software, and data working together to perform a task. That includes your laptop, sure — but it also includes the systems behind ATMs, the software managing your school’s grades, and the controllers that keep a power plant running safely.
Here are categories of systems that need cybersecurity protection, with examples of what happens when they are compromised.
Personal Devices and Home Networks
This is the layer closest to you — your phone, laptop, tablet, gaming console, and home Wi-Fi router. These devices store your personal information: photos, messages, passwords, financial data (if you shop online), and location history.
Why protect them?
- Identity theft: a stolen Social Security number or birthdate can be used to open credit cards in your name
- Financial loss: access to payment apps or saved credit cards means direct theft
- Privacy invasion: personal photos, messages, and browsing history exposed to strangers
- Botnet recruitment: compromised devices can be secretly used to attack other systems
Business and Enterprise Systems
Companies and organizations run computer systems that store customer data, process financial transactions, manage inventory, and coordinate employees. A single breach can expose millions of people’s personal information.
Why protect them?
- Customer data protection: names, addresses, credit cards, and Social Security numbers for millions of people
- Financial systems: direct access to money, payment processing, and banking transactions
- Intellectual property: trade secrets, product designs, and competitive advantages worth billions
- Operational continuity: a company that cannot access its own systems cannot serve its customers
Think about the businesses you interact with — your doctor’s office (medical records), your school (grades, personal info), your favorite online store (payment details). Every one of those organizations must protect the data you have entrusted to them.
Critical Infrastructure
This is where cybersecurity becomes a matter of life and death. Critical infrastructure refers to the systems that keep society functioning: power grids, water treatment plants, hospitals, transportation networks, and emergency services.
Why protect them?
- Power grids: a cyberattack on the electrical grid could leave entire cities without power for days or weeks
- Water systems: attackers could tamper with chemical levels in water treatment, making drinking water unsafe
- Hospitals: ransomware has forced hospitals to turn away patients, delay surgeries, and lose access to medical records
- Transportation: air traffic control, train switching systems, and traffic signals all run on computer systems
Choosing Your Three for Your Counselor
The requirement asks you to describe three types and explain why they need protection. You can pick from the categories above or identify your own — government systems, military networks, financial markets, educational institutions, and healthcare systems are all valid choices.
For each one, be ready to explain:
- What the system does — its purpose and what data it handles
- What could go wrong — specific consequences of a successful attack
- Who is affected — not just the organization, but the people who depend on it