Req 4a — Threats & Vulnerabilities
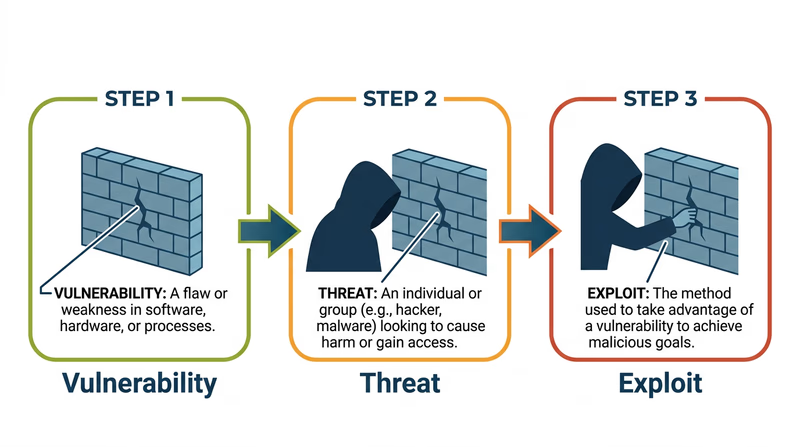
These three words — vulnerability, threat, and exploit — are the building blocks of cybersecurity language. Every attack, every defense, every news story about a breach comes back to these concepts. Understanding how they fit together is like learning the basic vocabulary of a new language.
Vulnerability
A vulnerability is a weakness or flaw in a system that could be used to cause harm. It is a door left unlocked, a window with a broken latch, a gap in the fence. The vulnerability exists whether or not anyone takes advantage of it.
Examples:
- A website that does not require strong passwords (allowing passwords like “123456”)
- Software that has not been updated and contains a known bug
- A Wi-Fi network that uses outdated encryption
- An app that stores passwords in plain text instead of encrypting them
Think of a vulnerability like a crack in a dam. The crack may sit there for years without causing a flood — but it is always a risk.
Threat
A threat is anything that could exploit a vulnerability to cause damage. Threats can be people (hackers, disgruntled employees), software (malware, ransomware), or events (natural disasters that knock out data centers). A threat is the potential for harm — the person who might notice that unlocked door.
Examples:
- A hacker scanning websites for known vulnerabilities
- A phishing email designed to trick you into revealing your password
- A disgruntled employee who still has access to company systems after being fired
- A power outage that crashes servers without proper backup
Exploit
An exploit is the actual method or action used to take advantage of a vulnerability. It is the moment the unlocked door gets opened. An exploit turns a theoretical risk into a real attack.
Examples:
- A piece of code that takes advantage of a software bug to gain unauthorized access
- Using a stolen password (the vulnerability was weak password requirements) to log into someone’s account
- Sending a specially crafted message to a website’s login form that tricks it into revealing database contents (called a SQL injection)
- Using a known Wi-Fi vulnerability to intercept someone’s data on a public network
How They Fit Together
The relationship is sequential:
- A vulnerability exists (a flaw or weakness)
- A threat recognizes the vulnerability (someone or something that could cause harm)
- An exploit takes advantage of it (the actual attack)
Here is a concrete example using a website you might use:
| Concept | Social Media Example |
|---|---|
| Vulnerability | The site allows unlimited login attempts with no lockout |
| Threat | An attacker with a list of common passwords |
| Exploit | The attacker runs an automated program that tries thousands of passwords against your account until one works (called a brute force attack) |
And another example:
| Concept | Gaming Platform Example |
|---|---|
| Vulnerability | The game’s chat system does not filter links |
| Threat | A scammer who creates fake “free V-Bucks” websites |
| Exploit | The scammer posts links in game chat; players who click enter their login credentials on a fake site, giving the scammer their accounts |
Applying This to Your Life
For your counselor, think about a website or app you actually use. Walk through the three concepts:
- What vulnerability might it have?
- What threat could take advantage of it?
- What would the exploit look like in practice?
You do not need to find a real vulnerability — this is a thought exercise about understanding the concepts.
Hackers & Cyber Attacks — Crash Course Computer Science A fast-paced, entertaining overview of how cyber attacks work from the Crash Course team.